AI and Ecommerce Website Security: How to Stay Ahead with Best Practices

Security threats often evolve faster than the systems built to stop them. In this article, we explore the patterns behind ecommerce vulnerabilities and how AI is redefining both risk and protection. And if you’re wondering where to start, contact our experts.
Reading time: 16 min.
IntexSoft experts are confident that in today’s AI-fueled gold rush, security is becoming the key factor in maintaining sustainable growth. Many of our clients have identified sustainability as a business priority.
We talk about security in e-commerce as if it’s a checklist — SSL here, a payment gateway there, a line about GDPR tucked quietly into the footer. But behind these measures is something more uncertain: the unspoken fear that none of it may ever be quite enough.
AI now powers recommendation engines, chatbots, supply chain logistics, and personalized pricing. These are the reasons why security has to evolve too. Because here’s the twist: as AI makes e-commerce smarter, faster, and more profitable — it also makes it more vulnerable.
Think about it. More data means more attack surfaces. More personalization means more sensitive information floating around. AI models — especially the black-box kind — introduce layers of risk most companies still don’t fully understand. And with cyber threats becoming more sophisticated by the hour, “hope for the best” is not a strategy.
A recent academic study from SRM Institute of Science and Humanities hits the nail on the head: AI is transforming everything from customer experience to inventory prediction — but also flags the very real dangers around data privacy, ethical use, and AI governance.
So why does this matter now?
Because trust is currency. Lose it, and it doesn’t matter how slick your UX is or how advanced your AI chatbot sounds. Customers won’t click “Buy Now” if they think their data’s walking out the back door.
Here’s what smart companies are doing: investing in AI-ready security infrastructure. Encrypting customer data. Running bias checks on their AI models. Adopting transparent AI frameworks. And, crucially, making security a boardroom issue — not just an IT problem.
Learn more details in this article.

What is in the center of the security story? Four pillars you have probably heard of — Privacy, Integrity, Authentication, and Non-repudiation. If you’re not nailing them, you’re playing defense with a blindfold on.
Now, let’s look at these 4 components and other essential ones.
Your customers are handing you not just their payment details, but a behavioral blueprint. And they expect ecommerce site security in return — whether they’re in New York, Oslo, or Warsaw. That’s why global standards like end-to-end encryption, secure browsing environments, cookie disclosure, and minimal data capture aren’t optional. AI makes personalization irresistible, but every “Hello, Sarah” email or customized homepage comes with a responsibility: don’t leak, don’t snoop, and don’t get sloppy.
The data you send or receive had better not be altered en route. You are sending an invoice or updating warehouse stock, and you have to be sure that it can’t be altered along the way. That’s what data integrity does. With tools like checksums and digital signatures, you get peace of mind that the information you send is exactly what’s received.
Two-factor authentication (2FA) is table stakes. Biometrics, hardware tokens, and behavioral analytics? That’s the new normal. If AI can predict buying patterns, it can also detect login anomalies. Use it.
Here’s where things get legal. Non-repudiation ensures that once a user makes a transaction, they can’t deny it later. Think digital receipts, tamper-proof logs, and cryptographic signatures. It is particularly helpful in cases of disputed chargebacks. Proof matters.
Not every employee needs access to your entire backend.
Systems don’t protect themselves. Access control frameworks like RBAC and IAM introduce logical boundaries, ensuring that permissions align with roles, not assumptions. When combined with least-privilege design, they minimize risk across a complex digital infrastructure.
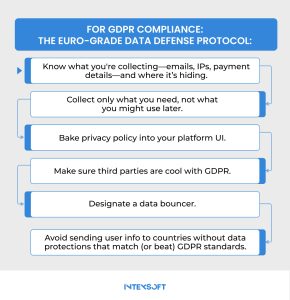
Data governance is your operating manual for digital responsibility. It’s also your best defense in a regulatory world tightening around GDPR, CCPA, and whatever comes next.
The truth is that breaches are inevitable. What matters is what you do next. The companies that stay out of the headlines have one thing in common — a damn good response plan, practiced and ready to fire. Real-time alerts, forensic tools, containment protocols secure your ecommerce brand.
There is a growing stack of security nightmares waiting to pounce. In e-commerce, every click, cookie, and credit card is a potential breach point.
Look at the table below. It’s a real rundown of today’s most pressing security challenges online store owners may face in practice.
| Challenge | What’s Happening Behind the Scenes | What It Really Means |
| Consumer Trust Is Cracking | Data breaches keep making headlines. Users are more cautious. Many don’t believe their personal data is safe anymore. | If people don’t trust the system, they won’t use it. That’s the beginning of the end for any online business. |
| Malware and Fraud Are Scaling Up | Sophisticated cyber tools — malware kits, phishing bots, and even AI — are now widely available. Bad actors move faster than most defenses. | This isn’t petty theft. It’s industrial-scale fraud. Businesses are getting hit — and many don’t even realize it. |
| Payment Systems Are Fragmented and Risky | Multiple payment processors, legacy platforms, inconsistent encryption. Few know who’s responsible when something breaks. | One weak link compromises the whole chain. And attackers know exactly where to look. |
| Authentication Still Rests on Passwords | Simple logins, reused passwords, no MFA. Despite the warnings, it’s still standard. | Breaches start with laziness. And businesses keep leaving the front door open. |
| Third-Party Plug-ins: Blind Spots in the Code | Businesses rely on outside tools — chatbots, CRMs, analytics — and rarely audit them for security. | These tools operate quietly. That’s exactly how threats slip in undetected. |
| Too Much Data, Not Enough Control | Companies collect everything. Few know what to protect or how. Governance often gets buried under growth goals. | Data without discipline becomes a liability. And the clock always runs out. |
| Mobile Apps Are the New Weak Point | Rapid development cycles and lax testing. Security updates often arrive too late — if at all. | Mobile traffic is rising. So are mobile threats. It’s a race, and businesses are behind. |
| Fake Signals, Real Consequences | Reviews can be faked. Identities spoofed. Hackers pose as staff. Customers can’t tell who to trust. | When credibility collapses, so does the brand. Perception is everything — and it’s easily manipulated. |
| Compliance Is a Moving Target | GDPR, CCPA, PCI-DSS — regulations keep evolving. Most firms don’t have a strategy, just checklists. | One misstep can cost millions. But many firms don’t realize until it’s too late. |
| Breaches Go Undetected for Weeks | No real-time monitoring. No clear plan. By the time they respond, the damage is done. | The breach isn’t the failure. The silence after is. Speed is survival — and most don’t have it. |
| Shadow IT and Unapproved Tools | Employees use unauthorized apps, cloud drives, AI tools, and messaging platforms to move faster. IT teams often don’t even know these systems exist. | Convenience creates invisible entry points. If it’s not monitored, it’s not protected. And attackers exploit what companies fail to see. |
Let’s break down the real threats — and why they’re hitting harder than ever.

Forget firewalls for a second. If someone can trick your customer — or worse, your employee — into handing over credentials, the rest is academic. In the past, phishing scams were laughably bad emails from mysterious princes, but today the picture has changed drastically. Phishing attacks are becoming hyper-targeted, AI-enhanced, and indistinguishable from genuine communication.
Some threats infect. Malware and ransomware are existential ones. One minute, your online shop is booming. The next? It’s offline, held hostage. Hackers inject malicious code through outdated plugins or stolen login credentials. The impact? Locked systems, stolen data, and paralyzed businesses. For many business owners, recovery comes with a price — literally.
SQL injection isn’t flashy. It doesn’t need to be. One wrong input field — left unsanitized by a developer — and an attacker can manipulate backend databases. We’re talking about unauthorized access to everything from inventory records to customer credit card numbers. And because the breach happens inside the system, it often goes unnoticed.
Hackers inject malicious scripts into trusted web pages, making them behave in rogue ways — like stealing session cookies, manipulating the UI, or redirecting users to sketchy domains. When an ecommerce site falls victim, it often leads to disaster.
Imagine someone standing between your customer and the payment processor, invisibly copying down every credit card detail. That’s e-skimming. Cybercriminal groups like Magecart inject malicious code into checkout pages, quietly harvesting payment information in real-time. It’s elegant. It’s elusive. And it’s causing billions in financial loss. Worse? It’s often discovered only after customer data is traded on the dark web.
The questions come fast: Is your ecommerce website protected? Is it protected at 3 a.m., when your team is asleep? Is it protected when a new vulnerability is discovered in a third-party plugin you haven’t updated?
These are not just ecommerce security best practices. They are lifelines. Implementing them means acknowledging that cyber threats are daily, evolving, and often invisible.
As we’ve seen time and again in interviews with CTOs and security leads, the companies that survive aren’t the ones with the biggest budgets. But the most vigilant.
Hackers have started turning the same machine learning breakthroughs driving Silicon Valley into tools of intrusion. AI models can now imitate user activity convincingly enough to bypass CAPTCHA, launch credential stuffing attacks, and mine sensitive information from thousands of websites.
That’s where the game changes. Because AI, while it’s a tool for intrusion, is also the key to defense. What separates the breached from the bulletproof is how you wield it.
Major platforms are now investing in AI for threat detection — behavioral analytics that learn what “normal” looks like on their site, then raise a red flag the moment something deviates. Not a human response — an automated one, delivered in milliseconds. It’s the ecommerce cyber attacks being blocked. It’s financial ruin being averted, customer trust being preserved, and lawsuits being dodged.
And the AI doesn’t sleep.
On the flip side, there’s automation designed to patch vulnerabilities before humans even notice them. Modern AI can perform continuous code scanning, recognizing patterns that indicate risk — like exposed APIs or misconfigured servers — and triggering updates before the breach happens. It’s a form of digital intuition, trained on millions of attacks.
The threats facing e-commerce platforms today are not exotic. They are familiar — DDoS attacks that flood systems, brute force logins that test the cracks in authentication, and SQL injections that quietly dismantle a database from within. These technical nuisances represent a growing failure to build resilient systems in an age when vulnerability can be monetized.
Despite an ever-evolving toolkit of cybersecurity solutions, billions are lost each year — not because online store owners don’t have the means to prevent it, but because, all too often, they don’t treat security for ecommerce website as a non-negotiable priority. Prevention still plays second fiddle to reaction.
This is where a shift in mindset is needed. Securing an e-commerce platform is a cyclical discipline — a repeated act of testing, identifying weaknesses, reinforcing them, and then testing again. It’s about understanding why online security is important to your business continuity, customer trust, and sustainable growth, as we have mentioned in the first part of this article.
The good news? You don’t have to face the chaos alone. IntexSoft‘s cybersecurity engineers can dive deep into your platform’s architecture to find the cracks — before someone else does.
Contact us anytime.